The SOC Is No Longer Human-First, And That Changes Everything
By Will Ledesma, Director of Global MDR Cybersecurity Operations, N-able
The modern Security Operations Center (SOC) is undergoing a quiet but fundamental shift that many organizations have yet to acknowledge: artificial intelligence is no longer just assisting analysts. It is now actively making decisions and executing them.
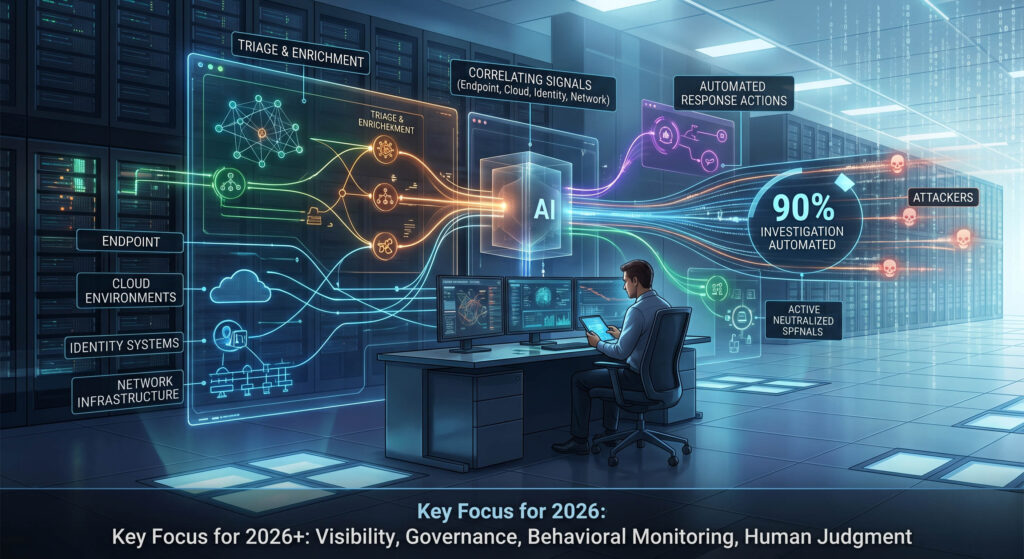
According to recent reports, AI is already automating up to 90% of investigation activity inside the SOC. In practice, this means that AI is now actively triaging alerts, correlating signals, initiating response actions, and in many cases acting as an always-on operator embedded directly within security workflows.
But this shift didn’t come from nowhere; it’s a response to the fact that traditional SOC models are reaching their limits in the AI-enabled threat environment.
The scale problem no human team can solve alone
SOC teams today are overwhelmed, understaffed, and increasingly outpaced by the speed and volume of modern attacks. Thanks to AI capabilities of their own, attackers are moving faster and blending into normal activity. Many attacks no longer rely on obvious malware or traditional indicators of compromise. Instead, they leverage legitimate tools like PowerShell, DNS, and standard system processes to operate in plain sight.
This creates a paradox: the more data security teams collect, the harder it becomes to identify what constitutes a legitimate threat. AI has become essential, not because it replaces humans, but because it operates at the speed and scale now required to make modern detection and response possible.
Correlation and context are the new frontier
One of the most important shifts happening inside the SOC is a move toward making signals usable at higher levels.
Modern attacks don’t stay confined to a single domain, but now move fluidly across identity systems, network infrastructure, cloud environments, and endpoints. Treating each signal independently creates noise, correlating them creates meaning.
This is especially critical as nearly half of observed attacks now bypass endpoints entirely, unfolding instead across network and perimeter layers. Without multi-layer visibility and automated correlation, these attacks remain invisible until it’s too late.
AI-driven detection changes this dynamic by combining multiple low-confidence signals (anomalous PowerShell usage, suspicious DNS behavior and unusual process execution) into a single, higher-confidence detection. The result is fewer alerts, and far more actionable ones.
As AI takes over repetitive, high-volume tasks such as triage, enrichment, and correlation, the role of the analyst is being reshaped. Instead of manually stitching together signals across identity, endpoint, network, and cloud layers, analysts are increasingly working with pre-correlated, high-confidence detections. This shift dramatically reduces noise and accelerates time-to-action.
As a result, signals are properly correlated across layers, allowing analysts to spend more time responding to confirmed threats. As we often say, analysts don’t need more data. They need more context. This is where AI delivers its greatest value: speed combined with clarity.
Rethinking security for an AI-driven SOC
This shift introduces new risk, as AI systems rely on data, models, and orchestration frameworks to inform their actions. If attackers can manipulate inputs, compromise orchestration layers, or mimic expected behavior, they can effectively hide within the system designed to detect them. In these scenarios, a compromised AI orchestrator could issue malicious commands at machine speed, amplifying the impact far beyond what a human attacker could achieve alone.
So, how should organizations adapt?
The first step is visibility, because you cannot hope to secure what you do not understand. Organizations need to inventory where AI is being used across security operations and what systems those AI agents can access.
The second step is governance. AI systems require clear controls around who – or what – can issue commands, how decisions are made, and the process by which those decisions are logged and audited. Decision traceability is critical, especially when actions are happening at machine speed.
Third is behavioral monitoring. Just as we baseline user behavior, we now need to baseline AI behavior. What does “normal” look like for an AI agent? When does it deviate? And how quickly can we detect that deviation?
Finally, and most importantly, human oversight remains essential. AI excels at speed and scale, but high-impact decisions still require human judgment. The goal is not to remove humans from the loop, but to elevate them to the positions where they can add the most value. Ideally, each AI tool should have both a technical and business owner ready to answer any questions about its abilities and level of access for all stakeholders involved.
The future of the human-led, AI-driven SOC
The SOC of the future won’t be human-only or AI-only. It should be a hybrid model where AI handles execution while humans provide direction. Organizations that embrace this model will gain a significant advantage in resilience overall: the advantage of speed over the full threat lifecycle.
The strongest cybersecurity posture of even just a year ago can no longer keep up. The pace is being continually reset by the need to detect threats earlier, respond faster, and maintain operations even under mounting pressure.
In 2026 and beyond, that level of resilience is only possible with AI as a core operational component. And as we integrate AI deeper into the SOC, we need to be clear-eyed about the trade-offs. AI is both a force multiplier and a potential vulnerability. Organizations must treat it as both.

Will Ledesma is Director of MDR Cybersecurity Operations at N-able, where he leads managed detection and response (MDR) strategy and oversees Security Operations Center (SOC) functions focused on AI-driven threat detection, incident response, automation, and cyber resilience. With deep expertise in SOC modernization, SOAR orchestration, threat hunting, and layered defense strategies, he regularly advises organizations on adapting security operations to combat increasingly sophisticated, AI-enabled cyber threats.